IoT devices are revolutionizing the way we interact with technology, but they also introduce new security challenges. Firewalls play a crucial role in safeguarding these devices from cyber threats. As the number of connected devices grows exponentially, understanding how to secure them becomes paramount.
The Internet of Things (IoT) has transformed industries and daily life, enabling devices to communicate and share data seamlessly. However, this interconnectedness exposes IoT devices to vulnerabilities that malicious actors can exploit. Implementing firewalls specifically designed for IoT devices is essential to protect sensitive information and maintain system integrity.
This article provides an in-depth exploration of firewall IoT devices, offering practical advice and expert insights. By the end, you'll have a comprehensive understanding of how firewalls function, why they're critical for IoT security, and how to implement them effectively.
Read also:Unveiling The Enigma Subrina Lucas Journey To Stardom
Table of Contents
- Introduction to IoT Firewalls
- The Importance of Firewalls in IoT Security
- Types of IoT Firewalls
- Implementing IoT Firewalls
- Benefits of Using Firewalls for IoT Devices
- Challenges in IoT Firewall Deployment
- Best Practices for Securing IoT Devices with Firewalls
- Case Studies: Real-World Examples
- Future Trends in IoT Firewall Technology
- Conclusion and Call to Action
Introduction to IoT Firewalls
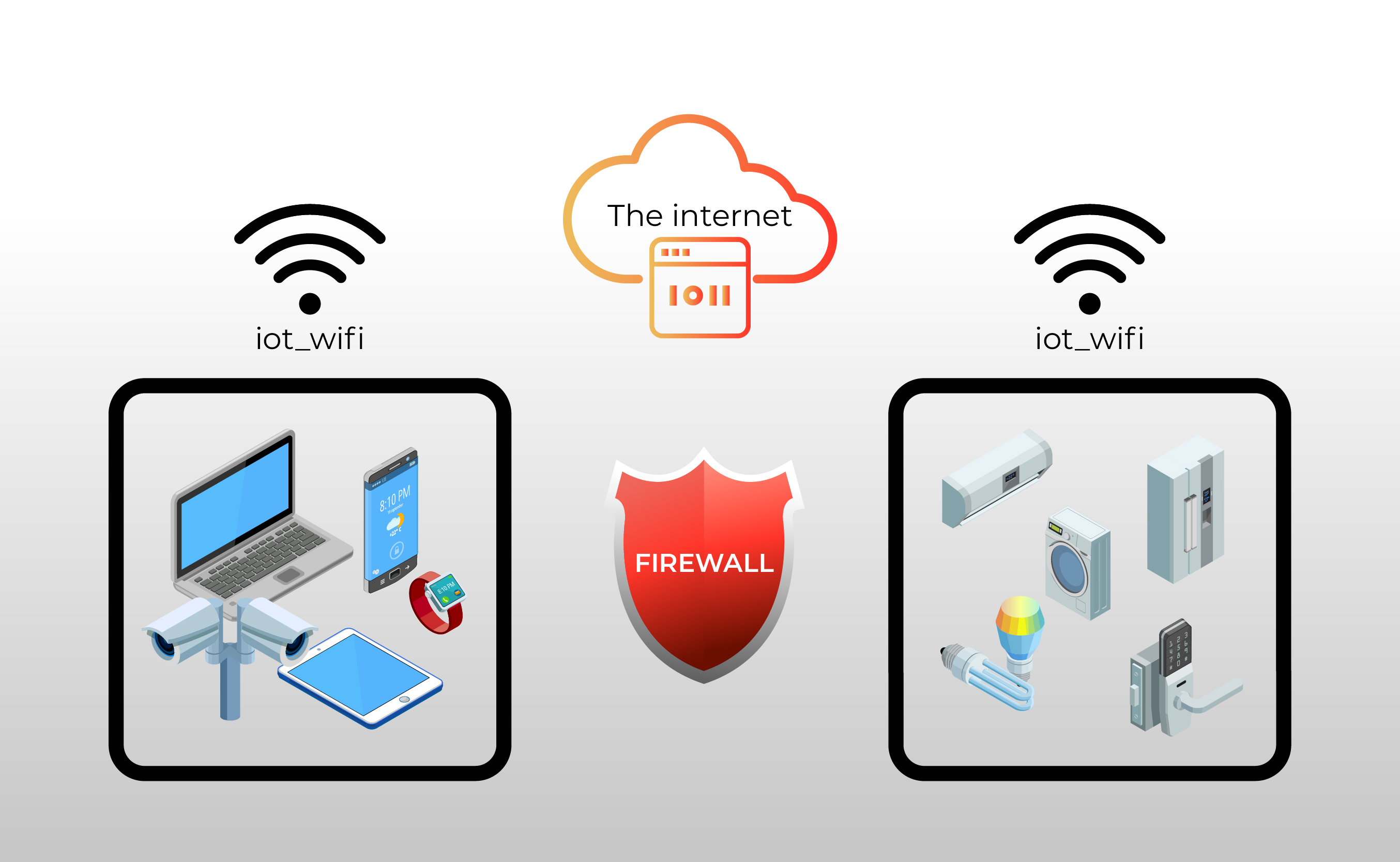
Firewalls have been a cornerstone of cybersecurity for decades, but their role in securing IoT devices is relatively new. IoT firewalls are specialized solutions designed to protect the unique architecture and communication protocols of IoT networks. Unlike traditional firewalls, IoT firewalls focus on lightweight, scalable solutions that can handle the vast number of devices and varying security requirements.
How IoT Firewalls Work
IoT firewalls operate by monitoring and controlling incoming and outgoing network traffic based on predetermined security rules. They analyze data packets, identify potential threats, and block unauthorized access. This process is critical for protecting IoT devices, which often lack robust built-in security features.
Key Features of IoT Firewalls
- Deep packet inspection for advanced threat detection
- Scalability to accommodate growing IoT networks
- Compatibility with various IoT protocols
- Real-time monitoring and alerting
The Importance of Firewalls in IoT Security
As IoT devices become more prevalent, so do the risks associated with them. Firewalls serve as the first line of defense against cyberattacks, protecting sensitive data and maintaining network integrity. Without proper firewall protection, IoT devices are vulnerable to unauthorized access, data breaches, and other security threats.
Statistical Evidence
According to a report by Gartner, the global IoT security market is expected to reach $3.1 billion by 2023. This growth highlights the increasing demand for robust security solutions, including firewalls, to protect IoT devices. Additionally, a study by Symantec found that 50% of all IoT devices are vulnerable to medium or high-severity attacks, emphasizing the need for effective firewall implementation.
Types of IoT Firewalls
IoT firewalls come in various forms, each tailored to specific use cases and requirements. Understanding the different types of firewalls can help organizations choose the right solution for their needs.
1. Hardware Firewalls
Hardware firewalls are physical devices that sit between the IoT network and the internet, providing dedicated protection. They are ideal for large-scale deployments where performance and reliability are critical.
Read also:Blue Ensign With Crown A Comprehensive Guide To Its History And Significance
2. Software Firewalls
Software firewalls are installed directly on IoT devices or servers, offering flexible and cost-effective protection. They are suitable for smaller networks or environments where hardware resources are limited.
3. Cloud-Based Firewalls
Cloud-based firewalls leverage the scalability and flexibility of cloud computing to provide comprehensive protection for IoT devices. They are particularly useful for organizations with distributed networks or those looking to reduce infrastructure costs.
Implementing IoT Firewalls
Successfully implementing an IoT firewall requires careful planning and execution. Here are some key steps to consider:
Step 1: Assess Your Network
Begin by evaluating your IoT network to identify potential vulnerabilities and security gaps. This assessment will help you determine the type of firewall and features needed for optimal protection.
Step 2: Choose the Right Solution
Select a firewall solution that aligns with your organization's size, budget, and security requirements. Consider factors such as scalability, ease of use, and compatibility with existing systems.
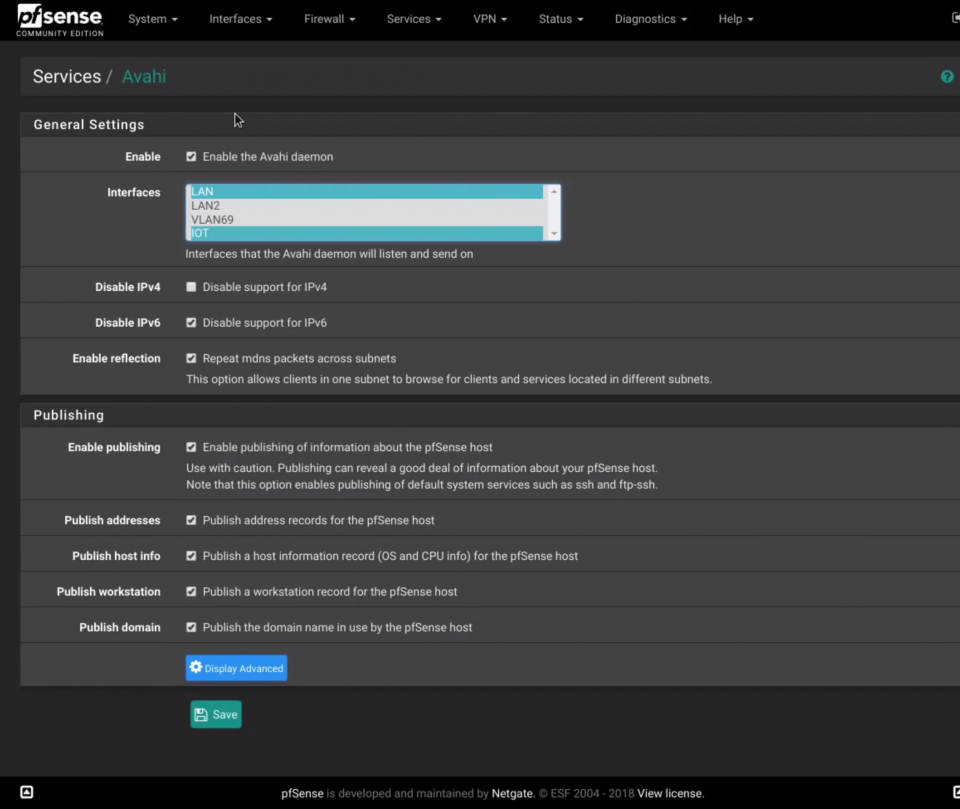
Step 3: Configure and Test
Once the firewall is installed, configure it according to your security policies and test its functionality to ensure it operates as intended. Regularly update and maintain the firewall to address emerging threats.
Benefits of Using Firewalls for IoT Devices
Implementing firewalls for IoT devices offers numerous benefits, including:
- Enhanced security against cyber threats
- Improved network performance and reliability
- Centralized management and control
- Compliance with industry regulations and standards
Challenges in IoT Firewall Deployment
While firewalls are essential for IoT security, their deployment can present challenges. Some common obstacles include:
Resource Constraints
IoT devices often have limited processing power and memory, making it difficult to implement resource-intensive firewalls. Lightweight solutions are necessary to overcome this limitation.
Interoperability Issues
Different IoT devices and protocols may not be fully compatible with certain firewall solutions, requiring additional configuration or customization.
Continuous Updates
Firewalls must be regularly updated to address new threats and vulnerabilities, which can be time-consuming and resource-intensive.
Best Practices for Securing IoT Devices with Firewalls
To maximize the effectiveness of IoT firewalls, follow these best practices:
- Regularly update firewall firmware and software
- Implement strong authentication and access controls
- Monitor network activity for suspicious behavior
- Segment IoT networks to isolate critical devices
Case Studies: Real-World Examples
Several organizations have successfully implemented IoT firewalls to enhance their security. For example, a healthcare provider used a cloud-based firewall to protect its IoT medical devices, reducing the risk of data breaches and ensuring compliance with HIPAA regulations. Another company in the manufacturing sector deployed hardware firewalls to secure its IoT-enabled production line, improving operational efficiency and reducing downtime.
Future Trends in IoT Firewall Technology
The future of IoT firewalls is promising, with advancements in artificial intelligence, machine learning, and edge computing driving innovation. These technologies will enable more intelligent and adaptive firewalls capable of detecting and responding to threats in real time.
AI-Powered Firewalls
AI-driven firewalls can analyze vast amounts of data to identify patterns and anomalies, providing proactive threat detection and response.
Edge Computing Integration
Integrating firewalls with edge computing devices allows for faster processing and reduced latency, enhancing the overall security of IoT networks.
Conclusion and Call to Action
In conclusion, firewalls are indispensable for securing IoT devices and protecting sensitive information. By understanding the different types of firewalls, implementing best practices, and staying informed about emerging trends, organizations can effectively safeguard their IoT networks.
We encourage you to take action by reviewing your current IoT security measures and considering the implementation of a firewall solution. Share your thoughts and experiences in the comments below, and explore our other articles for more insights into cybersecurity and IoT technology.