Remote access IoT behind router has become a crucial topic in the world of modern technology. As the Internet of Things (IoT) continues to expand, more devices are being connected to the internet, creating the need for secure and efficient remote access solutions. Whether for smart homes, industrial applications, or personal use, understanding how to access IoT devices remotely while ensuring security is vital for both users and developers.
In this article, we will explore the intricacies of remote access IoT behind router, covering everything from basic concepts to advanced techniques. By the end of this guide, you will have a thorough understanding of how to securely access IoT devices through routers, avoiding common pitfalls and ensuring optimal performance.
With the rise of remote work and smart technologies, the demand for reliable remote access solutions has never been higher. This guide will provide practical insights and actionable advice to help you navigate this complex yet fascinating field.
Read also:Barron Trump Sing A Fascinating Glimpse Into The Life Of The Trump Familys Youngest Member
Table of Contents
- Introduction to Remote Access IoT Behind Router
- Understanding the Basics of IoT Remote Access
- Setting Up Your Router for IoT Devices
- Ensuring Security in Remote Access
- Tools for Remote Access IoT
- Networking Concepts for IoT Devices
- Troubleshooting Common Issues
- Privacy Considerations in IoT Remote Access
- Applications of Remote Access IoT
- The Future of IoT Remote Access
Introduction to Remote Access IoT Behind Router
Remote access IoT behind router is a fundamental aspect of modern connectivity. IoT devices, ranging from smart thermostats to industrial sensors, require secure and stable connections to function effectively. Understanding how to access these devices remotely while maintaining security is essential for both personal and professional use.
The concept of remote access involves connecting to a device over the internet from a distant location. When it comes to IoT devices, this process can be complicated by firewalls, routers, and network configurations. However, with the right setup and tools, remote access can be achieved seamlessly.
This section will delve into the importance of remote access in IoT, its benefits, and the challenges associated with it. We will also explore how routers play a critical role in enabling secure access to IoT devices.
Understanding the Basics of IoT Remote Access
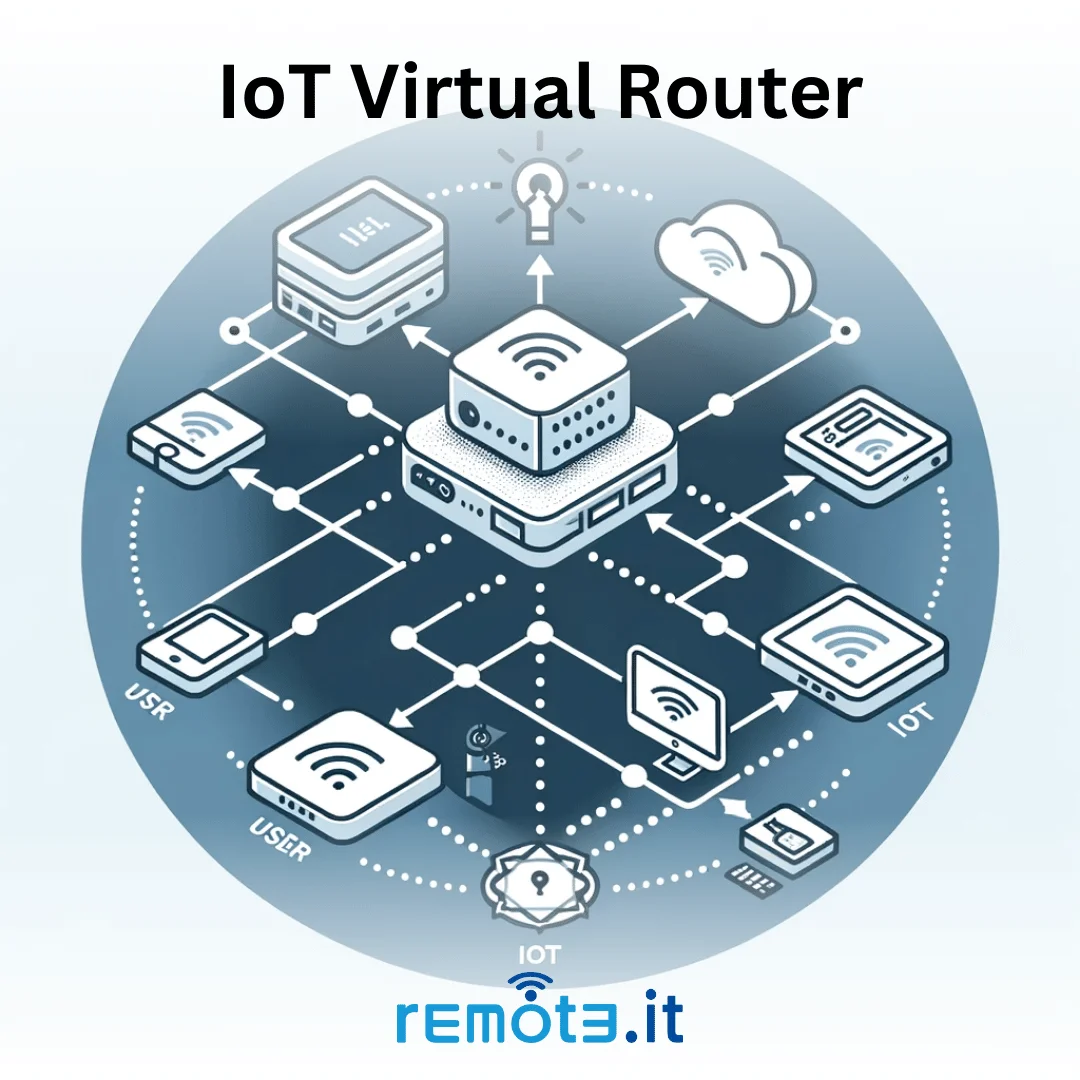
To fully grasp the concept of remote access IoT behind router, it is important to understand the basic principles involved. IoT devices are typically connected to local networks via routers, which act as gateways to the internet. These routers use Network Address Translation (NAT) to assign private IP addresses to devices within the network.
How IoT Devices Connect to the Internet
IoT devices connect to the internet through various means, including Wi-Fi, Ethernet, or cellular networks. Once connected, they communicate with cloud servers or other devices using protocols such as MQTT, HTTP, or CoAP. Understanding these communication protocols is essential for setting up remote access.
Key Components of Remote Access
- Router: Acts as the main gateway between the local network and the internet.
- Firewall: Protects the network from unauthorized access.
- Port Forwarding: Allows specific ports to be opened for external access.
- Dynamic DNS (DDNS): Provides a stable domain name for devices with dynamic IP addresses.
Setting Up Your Router for IoT Devices
Configuring your router properly is a crucial step in enabling remote access IoT behind router. This involves setting up port forwarding, enabling Dynamic DNS, and securing your network against potential threats.
Read also:Kelsie Frost A Rising Star In The World Of Entertainment
Port Forwarding
Port forwarding allows you to direct incoming traffic from the internet to specific devices on your local network. For example, if you want to access a smart camera remotely, you can forward the necessary ports (e.g., 80 for HTTP or 443 for HTTPS) to the camera's local IP address.
Dynamic DNS
Dynamic DNS (DDNS) is a service that maps your router's public IP address to a domain name. This is particularly useful if your ISP assigns dynamic IP addresses, as it ensures you can always reach your devices using the same domain name.
Securing Your Router
Security should be a top priority when setting up your router for IoT devices. This includes changing default passwords, enabling encryption, and regularly updating firmware to patch vulnerabilities.
Ensuring Security in Remote Access
Security is a critical concern when it comes to remote access IoT behind router. IoT devices are often targeted by hackers due to their relatively weak security measures. To protect your devices and network, it is essential to implement robust security protocols.
Best Practices for Securing IoT Devices
- Use strong, unique passwords for all devices.
- Enable two-factor authentication (2FA) whenever possible.
- Regularly update device firmware and software.
- Segment IoT devices on a separate network using VLANs.
Encryption and Authentication
Encrypting data transmitted between devices and using secure authentication methods can significantly enhance security. Protocols such as TLS (Transport Layer Security) and SSH (Secure Shell) provide secure communication channels for remote access.
Tools for Remote Access IoT
Several tools and platforms are available to facilitate remote access IoT behind router. These tools offer user-friendly interfaces and advanced features to simplify the process of connecting to IoT devices.
Popular Remote Access Tools
- TeamViewer: A versatile tool for remote access and support.
- LogMeIn: Offers secure remote access to computers and IoT devices.
- ngrok: Provides tunnels to expose local servers to the internet.
- Adafruit IO: A cloud platform for IoT projects with remote access capabilities.
Choosing the Right Tool
When selecting a remote access tool, consider factors such as ease of use, security features, and compatibility with your devices. It is also important to evaluate the cost and scalability of the solution to ensure it meets your needs.
Networking Concepts for IoT Devices
Understanding networking concepts is essential for setting up and managing IoT devices. This includes knowledge of IP addressing, subnetting, and network protocols.
IP Addressing
Each device on a network requires a unique IP address to communicate with others. IPv4 and IPv6 are the two main addressing schemes used today, with IPv6 offering a larger address space for future growth.
Network Protocols
Protocols such as TCP/IP, UDP, and ICMP form the foundation of internet communication. IoT devices often use specialized protocols like MQTT for lightweight messaging or CoAP for constrained environments.
Troubleshooting Common Issues
Despite careful planning and setup, issues may arise when attempting to access IoT devices remotely. Common problems include connectivity issues, security breaches, and configuration errors.
Steps to Troubleshoot
- Check router settings and ensure port forwarding is correctly configured.
- Verify that the device is connected to the network and has a valid IP address.
- Test the connection using tools like ping or traceroute.
- Review firewall rules and ensure they are not blocking necessary traffic.
Seeking Professional Help
If troubleshooting efforts fail, it may be necessary to consult a network specialist or seek support from the device manufacturer. Documenting the issue and providing relevant details can help expedite the resolution process.
Privacy Considerations in IoT Remote Access
Privacy is a growing concern in the age of IoT. Devices that collect sensitive data, such as cameras or health monitors, require special attention to ensure user privacy is protected.
Data Protection Measures
- Encrypt data at rest and in transit.
- Implement access controls to restrict who can view or modify data.
- Regularly audit data access logs for suspicious activity.
Compliance with Regulations
Compliance with data protection regulations such as GDPR or CCPA is essential for organizations handling personal data. Understanding and adhering to these regulations can help avoid legal issues and build trust with users.
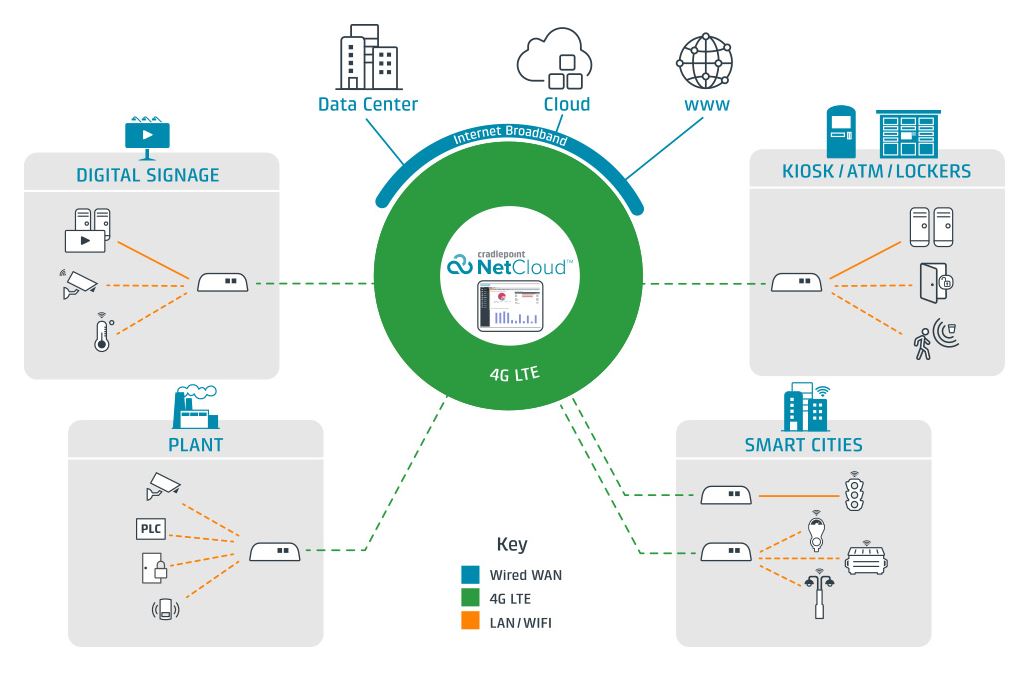
Applications of Remote Access IoT
Remote access IoT behind router has numerous applications across various industries. From smart homes to industrial automation, the ability to access devices remotely offers significant benefits.
Smart Home Automation
Remote access enables homeowners to control smart devices such as lighting, thermostats, and security systems from anywhere in the world. This convenience enhances lifestyle and improves energy efficiency.
Industrial IoT
In industrial settings, remote access allows engineers to monitor and control equipment in real-time, reducing downtime and improving productivity. This is particularly valuable in remote or hazardous environments where on-site access is limited.
The Future of IoT Remote Access
As technology continues to evolve, the future of IoT remote access looks promising. Emerging trends such as edge computing, 5G networks, and AI-driven analytics are set to revolutionize the way we interact with IoT devices.
Innovations in Remote Access
- Edge computing reduces latency by processing data closer to the source.
- 5G networks provide faster and more reliable connections for IoT devices.
- AI and machine learning enhance security and automation capabilities.
Challenges and Opportunities
While the future holds great potential, challenges such as security threats, interoperability issues, and privacy concerns must be addressed. By embracing innovation and adopting best practices, the IoT industry can unlock new possibilities and drive further growth.
Conclusion
In conclusion, remote access IoT behind router is a vital component of modern connectivity. By understanding the basics, configuring your router properly, and implementing robust security measures, you can ensure seamless and secure access to your IoT devices. The applications of remote access are vast, offering benefits across various industries and improving everyday life.
We encourage you to explore the tools and techniques discussed in this guide and apply them to your own projects. Share your thoughts and experiences in the comments below, and don't forget to check out our other articles for more insights into the world of IoT.